Identity and Access Management System Design
What We’ll Master Today
Authentication vs Authorization patterns and when each matters most
OAuth 2.0 flows that power Google, Facebook, and GitHub login systems
JWT token strategy and why Netflix moved away from them for certain use cases
RBAC vs ABAC decision framework used by enterprise systems
Zero Trust Architecture principles that transformed how we think about security perimeters
The $3.9 Billion Authentication Problem
When Equifax’s breach exposed 147 million records in 2017, the root cause wasn’t sophisticated hacking—it was a failure in identity and access management. A single unpatched web application component granted unauthorized access to their entire customer database. This incident crystallized a harsh reality: in distributed systems, identity management isn’t just a feature—it’s the foundation that determines whether your architecture stands or falls.
Modern applications don’t exist in isolation. Your e-commerce platform authenticates users, authorizes payment processing, integrates with third-party shipping APIs, and coordinates with recommendation engines. Each integration point becomes a potential security boundary that must be carefully managed without sacrificing user experience or system performance.
Authentication: Proving Who You Are
Authentication answers the fundamental question: “Who are you?” But in distributed systems, this simple question becomes surprisingly complex. Traditional username/password combinations work for monolithic applications but break down when users need seamless access across multiple services, mobile apps, and third-party integrations.
The Token Revolution: Modern systems use tokens instead of repeatedly validating credentials. When you log into Slack, you receive a token that proves your identity to their message service, file service, and notification service without re-entering your password dozens of times per day.
Multi-Factor Authentication (MFA) at Scale: Companies like Microsoft report that MFA blocks 99.9% of account compromise attempts. However, implementing MFA in distributed systems requires careful orchestration—each service must respect MFA decisions without forcing users to authenticate multiple times within a session.
JWT: The Double-Edged Sword
JSON Web Tokens (JWT) revolutionized distributed authentication by embedding user identity and permissions directly into the token. This eliminates database lookups for every request, dramatically improving performance. However, JWTs create a subtle trap that many systems fall into.
The Revocation Problem: Once issued, JWTs remain valid until expiration. If you need to immediately revoke a user’s access—perhaps they left the company or their account was compromised—you can’t simply “cancel” their JWT. Netflix discovered this limitation when they needed real-time access control for their content delivery network and implemented a hybrid approach combining short-lived JWTs with server-side session validation.
Authorization: Controlling What You Can Do
While authentication proves identity, authorization determines permissions. This distinction becomes critical in microservices architectures where each service must make independent authorization decisions without creating performance bottlenecks.
RBAC vs ABAC: The Strategic Choice
Role-Based Access Control (RBAC) assigns permissions to roles, then assigns roles to users. It’s simple to understand and implement—perfect for organizations with clear hierarchical structures. GitHub uses RBAC for repository access: users can be assigned “read,” “write,” or “admin” roles on specific repositories.
Attribute-Based Access Control (ABAC) makes authorization decisions based on attributes of the user, resource, and context. It’s more flexible but significantly more complex. Google Drive uses ABAC-like policies where document access depends on user attributes (employee status), resource attributes (document classification), and environmental attributes (access location, time of day).
The Hidden Insight: Most successful systems start with RBAC for simplicity, then migrate specific high-security areas to ABAC as needed. Attempting to implement ABAC from day one often leads to over-engineered systems that are difficult to debug and maintain.
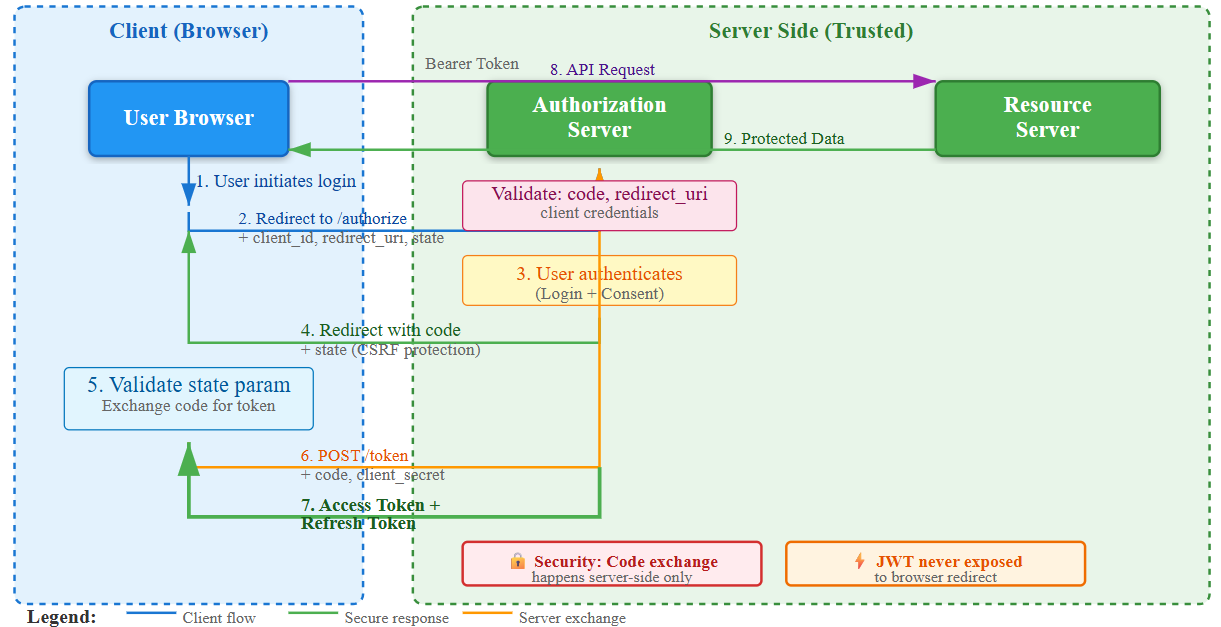
OAuth 2.0: The Internet’s Permission System
OAuth 2.0 powers the “Sign in with Google” buttons across the internet, but understanding its flow reveals deeper principles about secure authorization in distributed systems.